Journey Data: A New Paradigm in Fraud Fighting
In the digital age, where interactions between customers and brands unfold with every click, tap, and swipe, the integrity of these interactions is paramount. McKinsey sounded the alarm that innovation in both consumer digital experiences and attacker ecosystems have leapfrogged ahead of what reactive approaches to fraud fighting can manage without damaging the customer experience. Ecommerce fraud losses over the last year clocked in at a staggering $38B.
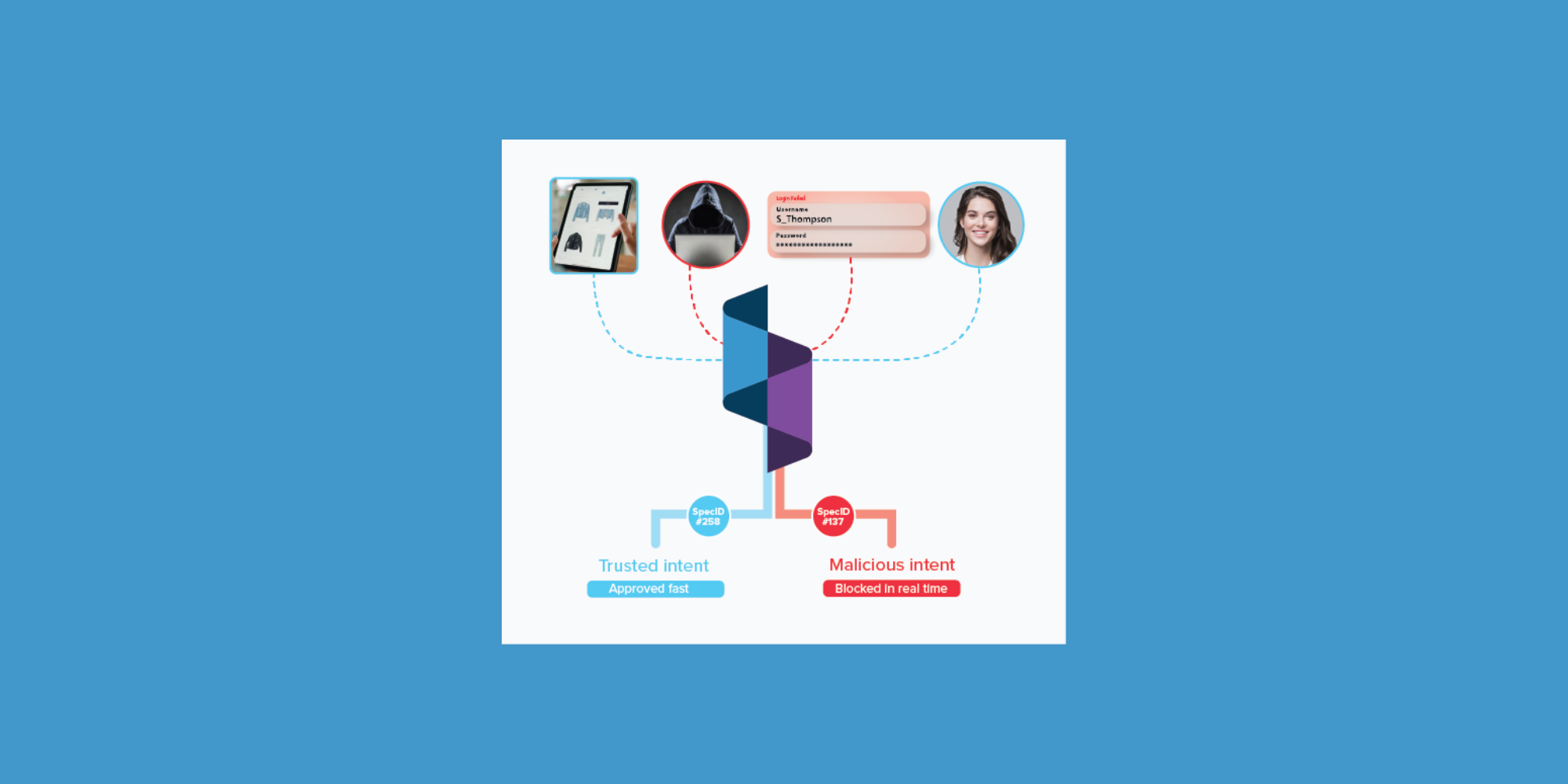
At Spec, we’ve pioneered a groundbreaking approach that positions Journey Data at the forefront of a proactive battle against fraud. Unlike traditional methods that are constrained to reacting to emerging attacks using fraud data alone, our strategy looks beyond these constraints to harness the full power of Journey Data. Businesses using Spec’s Customer Journey Security platform proactively identify and neutralize shifting fraud and abuse threats before they can have an impact, unlocking innovative customer experiences.
What is Journey Data?
Fraud teams have long been experts at analyzing transaction and login information to spot risks at checkpoints, but as attacker tools have evolved, these fraud rings have become experts at manipulating the data that fraud fighters rely on.
Journey Data brings together the behavioral data normally only available to Product teams, as well as the network data normally only available to Infosec teams, in order to paint a complete picture of the customer journey.

Journey Data is 14x larger than fraud data alone.
Collecting and linking all of this data to drive real-time decisions is a mammoth undertaking that’s beyond the reach of most businesses. Spec was built from the ground up to address this challenge head-on. Today, our platform protects innovative customer journeys that drive billions in commerce for our customers in marketplaces, ecommerce, and ticketing.
Why Now? Attackers Have a Data Advantage
The adoption of Journey Data for fraud defense has been driven by the rise in attacker sophistication. Legacy defenses rely on fraud data alone, and modern attackers have a broad set of tools to manipulate this data in order to evade detection.

The ability for attackers to effectively control the fraud data businesses rely on has turned what used to be a reactive but manageable game of whac-a-mole into a persistent problem that can derail major growth initiatives.
Journey Data takes the advantage away from attackers, as it forces users to actually be good customers in order to look like good customers.
Use Cases for Journey Data
Traditional approaches to fraud defense rely on a patchwork of point solutions to address risk at narrow checkpoints and leave gaps between these checkpoints for other types of fraud and abuse. Because Journey Data provides a comprehensive view of a user’s interactions with your website, it surfaces links, behavior, and data that identify malicious sessions in real time, regardless of the attacker’s tactics.
Enterprises typically start leveraging Journey Data to solve difficult problems that challenge their ability to deliver innovative customer experiences.

Beyond the core work of preventing online fraud, Journey Data enables fraud teams to communicate data-driven strategies that unlock greater profitability and growth to peer leaders of Marketing and Product teams.
Spec’s platform ensures that fraud teams are not working with just a piece of the puzzle, but with the entire picture. By harnessing the full scope of Journey Data, we’re not just responding to fraud; we’re anticipating and preventing it, setting a new standard in digital trust and security.
If you would like to see how Journey Data moves fraud teams past reactive fraud fighting and into the practice of understanding and proactively securing the customer journeys that power their business, contact us or request a private demo.